Alias/3 patch
- Thread starter Ginzanix
- Start date
It's tested only with Indy, I don't know if it works with other SGI models.
You can check your compleat ID from the sticker of backside near to power supply, it's someone similar to 080069123456. ( this is only for use your unique real addr ID ).
080069... is the same for all SGI, only change the last 6 numbers, now go to PROM monitor an type:
replace aa, bb, cc, dd, ee, ff for your ID.
fill -w -v 0xaa 0xbfbe04e8
fill -w -v 0xbb 0xbfbe04ec
fill -w -v 0xcc 0xbfbe04f0
fill -w -v 0xdd 0xbfbe04f4
fill -w -v 0xee 0xbfbe04f8
fill -w -v 0xff 0xbfbe04fc
Example for 080069123456
aa= 08
bb= 00
cc= 69
dd= 12
ee= 34
ff= 56
After type this commands reset your INDY and enjoy.
You can check your compleat ID from the sticker of backside near to power supply, it's someone similar to 080069123456. ( this is only for use your unique real addr ID ).
080069... is the same for all SGI, only change the last 6 numbers, now go to PROM monitor an type:
replace aa, bb, cc, dd, ee, ff for your ID.
fill -w -v 0xaa 0xbfbe04e8
fill -w -v 0xbb 0xbfbe04ec
fill -w -v 0xcc 0xbfbe04f0
fill -w -v 0xdd 0xbfbe04f4
fill -w -v 0xee 0xbfbe04f8
fill -w -v 0xff 0xbfbe04fc
Example for 080069123456
aa= 08
bb= 00
cc= 69
dd= 12
ee= 34
ff= 56
After type this commands reset your INDY and enjoy.
Last edited:
For the Indy it changes the value in NVRAM, i.e.When you change the sysID either by setenv or using the change sysID patch, does it “permanently“ change the sysID or does it reset after a reboot?
For the later systems the "feature" to change sysid was disabled, but it seems to work for the O2, however the sysid does not stick between reboots. According to some old newsgroup posts from a SGI employee, it was not intended to work with the O2 - it's a bug that it works at all...
ram...@hotmail.com writes:
| On the O2 systems, you can use
|
| setenv -f eaddr 08:00:69:xx:xx:xx
|
| and then just boot the system. it will stay with that eaddr as long as it's
| not powered off.
|
| i have tried this and it works.
It's a bug that it works...
For the original requestor, there is no such command, at least
for the systems that use the nvram eaddr as the basis for the
licensing serial number (the desktop machines, and some of the
servers). And no, I'm not just saying the party line; there really
isn't such a command.
--
Dave Olson, Silicon Graphics
http://reality.sgi.com/olson ol...@sgi.com
Last edited:
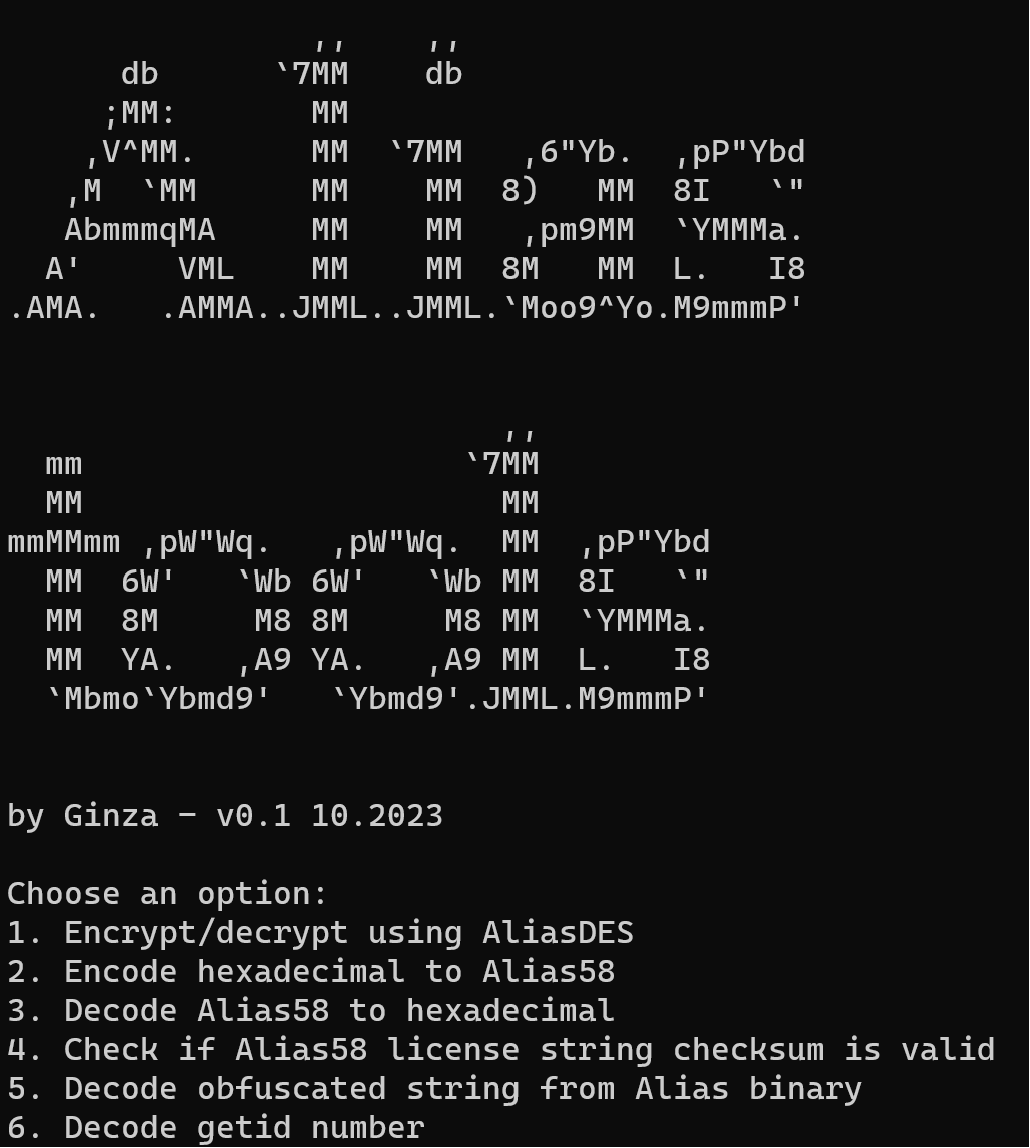
Thanks to our new overlord ChatGPT, and some not so insignificant additional research/debugging, I managed to understand the custom DES-encryption Alias used, and implement this together with the custom Base58 encoding and more in a C-program, even though I have no programming skills... amazing really! Please no complaints regarding program readability etc., though suggestions welcome. I will try to add some notes to the code later. Let me know if it compiles on Irix, which I have not yet tested, though I guess it should work.
Basically Alias used DES in OFB 1-bit mode (which is somewhat uncommon) to encrypt/decrypt licenses. In addition they added further layers of obfuscation by processing the encrypted string in reverse and more importantly by using bits from the plaintext to modify the IV for each round of decryption/encryption. This was probably so that a standard DES implementation could not be used if the keys and IV were discovered. The keys/IV are different for each version of Alias. I have not included the neccessary keys/IV in this program - you are prompted to provide them yourself. I didn't want to post keys here, to avoid any liability for the forum owner. However keys/IV can be read directly from the Alias binaries without too much work, and can probably be found online.
Basically this tool can help you to generate licenses (or decrypt existing licenses) for any sysid and any feature (if you provide the relevant IV/key and combine this with the license description here: https://wiki.preterhuman.net/Alias). It could easily be modified further to automate the whole thing. First encrypt the license string, then encode it to Alias58 (custom base58 variant). The program will generate the checksum and prefix character automatically. And there you have a valid license string for your SGI (and possibly IBM if you can find that rare version)...! In theory this applies to all versions back to the ones running on Irix 3 (I have tested Alias 3.1 at least), possibly even 2.4 versions, if they are ever found..!
There are a few other interesting discoveries related to this. Jan-jaap has previously noted that the findkey program uses DES to process an encrypted text file with all the Alias pre-keyed customers FlexLM licenses (at least from Alias 7.5 onwards). This text file can easily be decrypted, as it does not use the custom "AliasDES" DES OFB 1-bit implementation, but standard DES in CFB8 mode. You just need the IV and key again, which are quite easy to find. You can even use OpenSSL to decrypt ths file directly (enc -d -des-cfb8 -iv XXX -K XXX -in Alias.master -out Alias.master.decrypt).
The many pre-key licenses in this file have a format like this:
# prekey info for (getid = XX, sysinfo = XX)
FEATURE AW_A3D sgiawd 7.500 1-jan-0 0 XX\
VENDOR_STRING=A7KpP36tDjhknDriK8MmII HOSTID=XX ck=55
I was not sure what the VENDOR_STRING was, but after checking with my tool, it is clear that it is simply an Alias58 encoded string, without any encryption. Just remove the first character (version character) and last character (checksum character) and run it through the Alias58 decoder included, and you will get what seems to be the features enabled for this specific license. Seems Alias did not use individual FlexLM features at this point, and instead used the vendor string to check for features. I was curious if the vendor_string was actually the customer name, but unfortunately that doesn't seem to be the case...
Basically Alias used DES in OFB 1-bit mode (which is somewhat uncommon) to encrypt/decrypt licenses. In addition they added further layers of obfuscation by processing the encrypted string in reverse and more importantly by using bits from the plaintext to modify the IV for each round of decryption/encryption. This was probably so that a standard DES implementation could not be used if the keys and IV were discovered. The keys/IV are different for each version of Alias. I have not included the neccessary keys/IV in this program - you are prompted to provide them yourself. I didn't want to post keys here, to avoid any liability for the forum owner. However keys/IV can be read directly from the Alias binaries without too much work, and can probably be found online.
Basically this tool can help you to generate licenses (or decrypt existing licenses) for any sysid and any feature (if you provide the relevant IV/key and combine this with the license description here: https://wiki.preterhuman.net/Alias). It could easily be modified further to automate the whole thing. First encrypt the license string, then encode it to Alias58 (custom base58 variant). The program will generate the checksum and prefix character automatically. And there you have a valid license string for your SGI (and possibly IBM if you can find that rare version)...! In theory this applies to all versions back to the ones running on Irix 3 (I have tested Alias 3.1 at least), possibly even 2.4 versions, if they are ever found..!
There are a few other interesting discoveries related to this. Jan-jaap has previously noted that the findkey program uses DES to process an encrypted text file with all the Alias pre-keyed customers FlexLM licenses (at least from Alias 7.5 onwards). This text file can easily be decrypted, as it does not use the custom "AliasDES" DES OFB 1-bit implementation, but standard DES in CFB8 mode. You just need the IV and key again, which are quite easy to find. You can even use OpenSSL to decrypt ths file directly (enc -d -des-cfb8 -iv XXX -K XXX -in Alias.master -out Alias.master.decrypt).
The many pre-key licenses in this file have a format like this:
# prekey info for (getid = XX, sysinfo = XX)
FEATURE AW_A3D sgiawd 7.500 1-jan-0 0 XX\
VENDOR_STRING=A7KpP36tDjhknDriK8MmII HOSTID=XX ck=55
I was not sure what the VENDOR_STRING was, but after checking with my tool, it is clear that it is simply an Alias58 encoded string, without any encryption. Just remove the first character (version character) and last character (checksum character) and run it through the Alias58 decoder included, and you will get what seems to be the features enabled for this specific license. Seems Alias did not use individual FlexLM features at this point, and instead used the vendor string to check for features. I was curious if the vendor_string was actually the customer name, but unfortunately that doesn't seem to be the case...
Attachments
-
17.2 KB Views: 101
Last edited:
Here is a new and much updated version of Aliastools. In this version, license strings can be generated automatically - no more copy and pasting. Also added support for Alias Eclipse 1.0/1.1 and Alias Full Color Publisher 3.2. Finally I added support for enabling individual hardware features in the license. This is cumbersome but neccessary to pass the "host class" checks in Alias Power Animator versions 4.0 and earlier (also Full Color Publisher, but not Eclipse). For the "host class" check - your license must match exactly the hardware features reported for your computer when running "getid -i". You cannot simply enable all hardware features in the license, the hardware features are keyed to your specific SGI hardware. Not surprising that Alias removed the "host class" check in later versions - by changing the number of CPUs or graphics card, you would need a new license - something which probably generated lots of support calls.
Interestingly I discovered that the Indy is not officially supported by PA 4.0, and the sysid is reported as 00000000 and the "host class" features are all zeroed out. However, you can actually generate a "hostid any" license for PA 4.0 valid for any Indy, just by setting the sysid in the license as 00000000 and disabling all hardware features, seems to work fine...
Please note: the source code attached does not contain the actual Alias keys, just dummy keys - you will need to provide the keys yourself or find them somehow. The implementation is the difficult part, however, and I thought it would be useful to share publicly. If someone could test compiling this for Irix, or even implementing an IRIX GUI, that would be nice.
Interestingly I discovered that the Indy is not officially supported by PA 4.0, and the sysid is reported as 00000000 and the "host class" features are all zeroed out. However, you can actually generate a "hostid any" license for PA 4.0 valid for any Indy, just by setting the sysid in the license as 00000000 and disabling all hardware features, seems to work fine...
Please note: the source code attached does not contain the actual Alias keys, just dummy keys - you will need to provide the keys yourself or find them somehow. The implementation is the difficult part, however, and I thought it would be useful to share publicly. If someone could test compiling this for Irix, or even implementing an IRIX GUI, that would be nice.
Attachments
-
97.8 KB Views: 82
